Bezpečnostní nástroje ExpressVPN
How to use the WebRTC leak checker
What’s the difference between public and local IP addresses?
When you use the leak checker you’ll see two classes of IP addresses displayed: public and local.
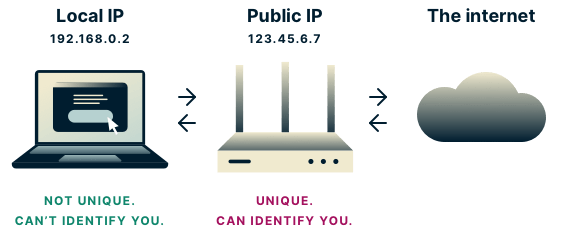
Public IPs are highly specific to you. They form part of your identity on the internet. When you use a VPN, sites see the VPN server’s public IP address instead of yours, and your identity is protected.
However, if WebRTC detects your real public IP address when you’re connected to a VPN, as opposed to the VPN server’s, then third parties can still use it to identify you. If you see a public IP in the test results, then you may have a privacy leak.
Local IPs are not specific to you. These IPs are assigned to you by your router and are reused millions of times by routers all over the world. So if a third party knows your local IP address, it has no way of linking it directly to you. If you see a local IP in the test results, it is not a threat to your privacy.
5 steps to test for a WebRTC leak (with and without VPN)
If you’re not using a VPN you will undoubtedly be exposing some private information to third parties. (Want to learn more? See how a VPN hides your IP address to keep your information private.)
If you are using a VPN and the leak tool indicates there may be a leak, then you can perform the following leak test to be sure:
-
Disconnect from your VPN and open this page in a new tab or window
-
Make a note of any public IP addresses you see
-
Close the page
-
Connect to your VPN and reopen the page
-
If you still see any of the public IP addresses from Step 2, then you have a privacy leak
If you’re using a VPN and the tool specifically tells you there is no leak, you’re safe!
Want to check for other privacy leaks? Try these tools:
What is WebRTC?
Web Real-Time Communication (WebRTC) is a collection of standardized technologies that allows web browsers to communicate with each other directly without the need for an intermediate server. Benefits of WebRTC include: faster speeds and less lag for web apps like video chat, file transfer, and live streaming.
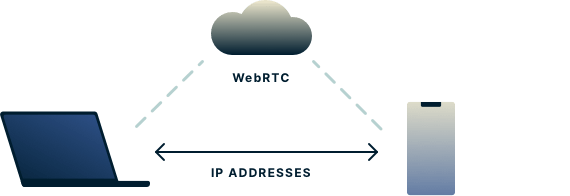
Any two devices talking to each other directly via WebRTC, however, need to know each other’s real IP addresses. In theory this could allow a third-party website to exploit the WebRTC in your browser to detect your real IP address and use it to identify you. This is what we call a WebRTC leak.
Any leak of your public IP address is a threat to your privacy, but WebRTC leaks are lesser-known and easily overlooked, and not all VPN providers protect you from them!
How does a WebRTC leak put my privacy at risk?
The problem with WebRTC is that it uses techniques to discover your IP addresses that are more advanced than those used in “standard” IP detection.
How does WebRTC detect my IPs?
WebRTC discovers IPs via the Interactive Connectivity Establishment (ICE) protocol. This protocol specifies several techniques for discovering IPs, two of which are covered below.
STUN/TURN servers
STUN/TURN servers play two key roles in WebRTC: They allow web browsers to ask the question “What are my public IPs?” and they also facilitate two devices talking to each other even if they are behind NAT firewalls. The former is the one that can affect your privacy. STUN/TURN servers discover your IPs much as a website sees your IPs when you visit it.
Host candidate discovery
Most devices have multiple IP addresses associated with their hardware. Usually these are hidden from websites and STUN/TURN servers via firewalls. However, the ICE protocol specifies that browsers can gather these IPs simply by reading them off your device.
The IPs most commonly associated with your device are local IPv4 addresses, and discovery of them won’t affect your privacy. If you have IPv6 addresses, however, then your privacy could be at risk.
IPv6 addresses don’t work quite the same as IPv4 addresses. Generally, an IPv6 address is a public one (which means it is unique to you). If you have an IPv6 address associated with your device, and it is discovered via ICE, then your privacy could be exposed.
A malicious website could use STUN/TURN servers or host candidate discovery to trick your browser into revealing an IP address that could identify you, all without your knowledge.
WebRTC leaks: Which browsers are most vulnerable?
As of this writing, users of Firefox, Chrome, Opera, and Microsoft Edge are most vulnerable to WebRTC leaks because these browsers have WebRTC enabled by default.
Note that you may be safe from WebRTC leaks in one browser and not in another. If you regularly use multiple browsers, then you should consider using the ExpressVPN WebRTC Leak Test on each of them.
What does ExpressVPN do to protect me from WebRTC leaks?
ExpressVPN works hard to ensure its apps protect you from WebRTC leaks. When you open new web pages while connected to ExpressVPN, your public IP addresses won’t leak.
Some browsers, however, can be aggressive when it comes to holding onto data from old tabs. If you have a tab open from before you connected to the VPN, your real IP address may be cached in memory by the browser. These IPs can persist even if you refresh the tab, which puts your privacy at risk.
The ExpressVPN browser extension (currently available for Chrome, Firefox, and Edge) solves this problem by letting you completely disable WebRTC from the settings menu, which will ensure that you’re not vulnerable to any caching issues.
How ExpressVPN’s dedicated leak-proofing engineers keep you safe
ExpressVPN protects you from a wide spectrum of WebRTC leaks across different browsers and platforms. Because WebRTC is still a relatively new technology, it’s important to continually test different scenarios for WebRTC leaks across different platforms and browsers. ExpressVPN leads the industry with a team of dedicated engineers who constantly investigate new leak vectors and rapidly develop any necessary fixes.
Learn more about ExpressVPN’s latest leak-proofing developments.
How else can I prevent WebRTC leaks?
In addition to using ExpressVPN, you may be able to guard against leaks by manually disabling WebRTC in your browser.*
How to disable WebRTC in Firefox on desktop
- Type about:config into the address bar
- Click the “I accept the risk!” button that appears
- Type media.peerconnection.enabled in the search bar
- Double-click to change the Value to “false”
This should work on both mobile and desktop versions of Firefox.
How to disable WebRTC in Chrome on desktop
There are two Chrome extensions known to successfully block WebRTC leaks:
uBlock Origin is a general all-purpose blocker that blocks ads, trackers, malware, and has an option to block WebRTC. WebRTC Network Limiter is an official Google add-on that specifically stops IP leaks without totally blocking WebRTC.
How to disable WebRTC in Safari on desktop
There’s no need to disable WebRTC in Safari. Safari’s permissions model is stricter than those of most browsers. By default, no IP addresses are made available to websites except the one you use to access the site. Therefore you shouldn’t need to take any additional action to prevent WebRTC leaks in Safari. Note, however, that if you grant any particular site permission to use audio or video capture, you might expose your IPs.
How to disable WebRTC in Opera on desktop
- Open Settings in Opera. To do this:
- On Windows or Linux, click the Opera logo at the top-left corner of the browser window
- On Mac, click Opera in the toolbar and locate settings under Preferences
- Expand the Advanced section on the left-hand side and click Privacy & security
- Scroll down to WebRTC and select the Disable non-proxied UDP radio button
- Close the tab and the settings should automatically save
How to disable WebRTC in Microsoft Edge
Unfortunately, there’s currently no way to completely disable WebRTC in Microsoft Edge. However, you can set your browser to hide your local IP address if you:
- Type about:flags into the address bar
- Check the option marked Hide my local IP address over WebRTC connections
As mentioned above, revealing your local IP address is not a threat to your privacy, so the steps above offer little benefit. Therefore the best way to stop WebRTC leaks while using Microsoft Edge is by using the ExpressVPN app for Windows.
*Disabling WebRTC probably won’t affect normal web browsing. Most websites don’t depend on it… yet. But as WebRTC becomes more popular, the functionality of certain sites may decline if you disable it completely.
What if I’m connected to ExpressVPN, and I still see a WebRTC leak on this page?
Contact ExpressVPN Support, and we’ll get that sorted out promptly.